Background
Looking back a few years deploying ADFS as a pre-requisite to your Office 365 migration was pretty much standard. For companies without existing ADFS farms deploying ADFS servers as well as Web Application Proxies created a lot of extra administration that the cloud investment was meant to reduce.

With the introduction of Password Synchronization in Azure AD Connect it may be worth considering decommissioning your (fairly) new ADFS farm in favor of something a bit more hands-off.
FAQ
Is password synchronization safe?
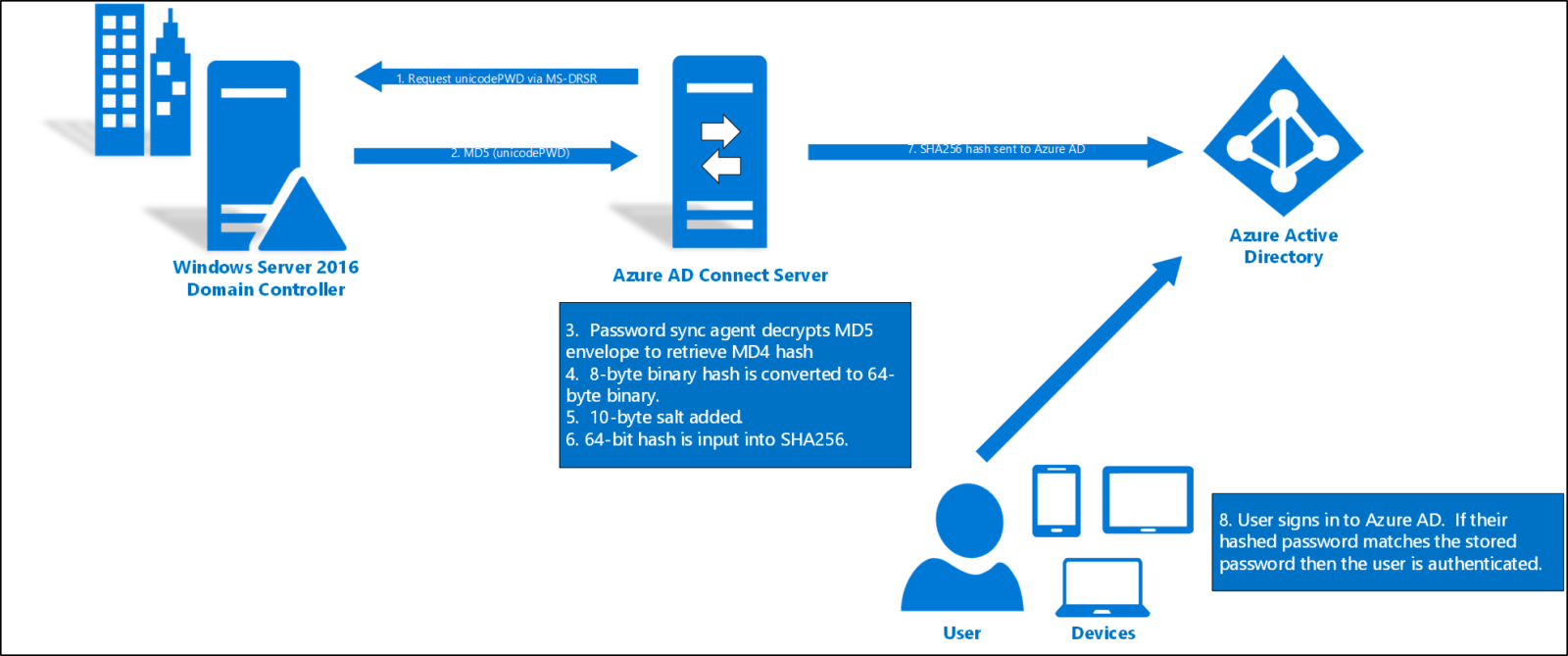
The password synchronization service in Azure AD Connect doesn’t actually sync your password to Azure AD. When enabled the service will hash the password hash from Active Directory essentially syncing a hash of a hash.
If the hash would somehow become publicly known it’s really down to the complexity of the password. A simple password may be cracked in minutes while a complex password could take years. Regardless it’s always recommended to use multi-factor authentication to keep your account safe.
In summary a substantial data leak from Microsoft would be required to even make the hashed hashes available and a leak wouldn’t necessarily mean that your accounts are immediately compromised. With these things in mind you need to consider your internal IT-security as well as other attack vectors to make your choice.
We use ADFS for other services, is it worth the change?
- One of the main advantages of moving away from ADFS is that the dependency on PaaS or even on premise solutions is removed from the equation. Even if your entire datacenter is dead your users would still be able to access Office 365 services.
- Features are constantly being added to Azure AD to allow support for your currently federated applications. It is likely that a fair number of your current applications can be moved from ADFS today reducing the criticality of your remaining ADFS farm.
- Microsoft are part of the FIDO-alliance and password-less authentication is currently in private preview with an expected public preview in Q1 2019. Microsoft will release the capabilities to customer using Azure AD for their authentication first. While support is likely to become available for ADFS later on, if you want to adopt this technology quickly password synchronization is the way to go.
Testing
As with any major change it is recommended to start out with some controlled testing. Can this be done with password synchronization? The answer is yes and no.
Enabling password synchronization in Azure AD Connect will sync the passwords of all users handled by the sync engine essentially making it on or off for all users this however does not impact user authentication in any way. After enabling password sync your users will still authenticate through ADFS.
When the passwords are synced you can change the authentication method on a per-domain basis. The domain affected is the one used in your users UPN. Please note that the authentication method used by a sub-domain must be the same as the base domain.
To perform testing for a limited number of users you may convert one of your domains currently in use or add a new domain to AD and Office 365. If you opt for a new domain, don’t configure it for federation. After adding the domain all you need to do is change the UPN of the users involved in the pilot and they will sign in without ADFS.
This post is incomplete, hopefully it was still somewhat useful. I may add details about implementation next time I perform this change in a production environment.
If you have questions feel free to leave a comment or contact me: martin[at]technut.se